
Threat Alerts
SharePoint Vulnerability CVE-2025-53770.
Microsoft is aware of active attacks targeting on-premises SharePoint Server customers by exploiting vulnerabilities partially addressed by the July Security Update. Read the guidance from Microsoft regarding SharePoint vulnerability CVE-2025-53770.
Blogs
Remote Access Tools 2025: Security and Productivity
As businesses continue to embrace remote work and digital collaboration in 2025, Remote Access Tools (RATs) have become essential for maintaining productivity and supporting distributed teams. Yet, these powerful platforms also present a growing security challenge, as cybercriminals increasingly exploit vulnerabilities, misconfigurations, and user trust to infiltrate networks.

Threat Alerts
Next-Gen Threats: How Cybercriminals Are Exploiting AI
Generative AI is rapidly reshaping the cybercrime landscape, enabling threat actors to launch faster, more convincing, and highly scalable attacks. As defenders explore AI for productivity and automation, cybercriminals are exploiting the same tools to streamline fraud, malware development, phishing, and vulnerability exploitation.
Blogs
Lumma Stealer Using Legitimate Windows Tools Tactics
Lumma Stealer—a powerful information-stealing malware that has wreaked havoc across the globe—made headlines in 2025. The Malware-as-a-Service (MaaS) platform, also known as LummaC2, allows cybercriminals to rent and deploy malware designed to steal sensitive information from infected devices. First surfacing in 2022, it has rapidly evolved into one of the most notorious info stealers on the dark web.

Threat Alerts
Astaroth Phishing Tool Bypasses Two-Factor Authentication
A new phishing tool called Astaroth threatens the security of online accounts globally. This malicious tool bypasses two-factor authentication (2FA), which is meant to be a vital layer of protection for private accounts, enabling hackers to steal sensitive information such as usernames, passwords, credit card details, bank information, and more.

Threat Alerts
CISA Releases Malware Report On RESURGE Malware
On Friday March 28, 2025 CISA released a report with analysis of a new malware variant CISA has identified and named as RESURGE. RESURGE is a persistent malware that shares similar characteristics to the malware SPAWNCHIMERA. Please review the information that is taken directly from CISA and compiled by DefenseStorm Director of Cyber Threat Intelligence to learn more about RESURGE, its capabilities, and attack vectors.

Threat Alerts
Business Email Compromise Threats on the Rise
Business Email Compromise (BEC) is a sophisticated email scam where cybercriminals trick victims into transferring funds or sharing sensitive data. Learn more about common BEC attack types, how they work, and essential strategies for protection.

Threat Alerts
M365 Password Spraying Attack via Botnet
Microsoft 365 accounts are facing an extensive password spraying attack by a Chinese botnet, which possesses the ability to bypass multifactor authentication (MFA). This botnet comprises over 130,000 compromised devices, utilizing stolen credentials from infostealer accounts and then systematically attempting to log into M365 accounts globally.

Blogs
Lazarus Group’s LinkedIn Job Offer Scam Exposed
With recruiters using LinkedIn as a very popular way to research and reach out to potential candidates, bad actors have begun to try to abuse people’s trust and desire for new challenges to lure them in with fake job opportunities as a way capture their credentials and deliver additional malware.
Blogs
Tax Season IRS Tips for Scams
The IRS has already made several reminders for individuals to be aware of bad actors trying to take advantage of this season to gain access to your personal data and finances. Read tips and guidance taken directly from the IRS’ website, including associated links to stay safe during tax season.

Blogs
NIST Framework Password Recommendations
Take a minute and think about the password(s) you use in both your professional and personal capacities. When passwords are reused or weak, they are far more susceptible to being stolen. One stolen password can lead to a detrimental data breach for your organization.

Blogs
Post-FFIEC Cybersecurity: Strategies for Stronger Defense
To prepare for the FFIEC Cybersecurity Assessment Tool sunset date, financial institutions should identify a new framework around which to build their programs and self-assess themselves against that framework using a risk based approach to ascertain that the appropriate level of maturity is reached within various areas.

Threat Alerts
Black Friday & Cyber Monday: Rising Cyber Risks
As the excitement of Black Friday and Cyber Monday draws shoppers in with unbeatable deals and discounts, it’s important to remember that the online shopping frenzy also brings increased cybersecurity risks.

Blogs
Remote Access Tools: Friend or Foe?
With the remote workforce not showing any signs of slowing down, many organizations are starting to evaluate and implement ways to access these systems through the usage of Remote Access Tools. While these tools provide an incredible amount of value to an organization to stay connected and retain access, Remote Access Tools are a significant attack vector in cybersecurity and are something that should not be taken lightly.

Webinars & Videos
Rodney Hood emphasizes the importance of enhancing risk management practices
DefenseStorm Board member and former chairman of the NCUA, Rodney Hood emphasizes the importance of enhancing risk management practices for financial institutions, urging them to extend their risk disciplines to cybersecurity and information security. He highlights the necessity of conducting thorough risk assessments in-house, defining risk appetite, and establishing meaningful metrics to foster effective governance and prepare for evolving risks.

Threat Alerts
CISA Warns of Hurricane-Related Scams
CISA is alerting the public to be cautious of potential cyber scams following hurricanes. After major natural disasters, fraudulent emails and social media messages—often containing harmful links or attachments—are common.
Blogs
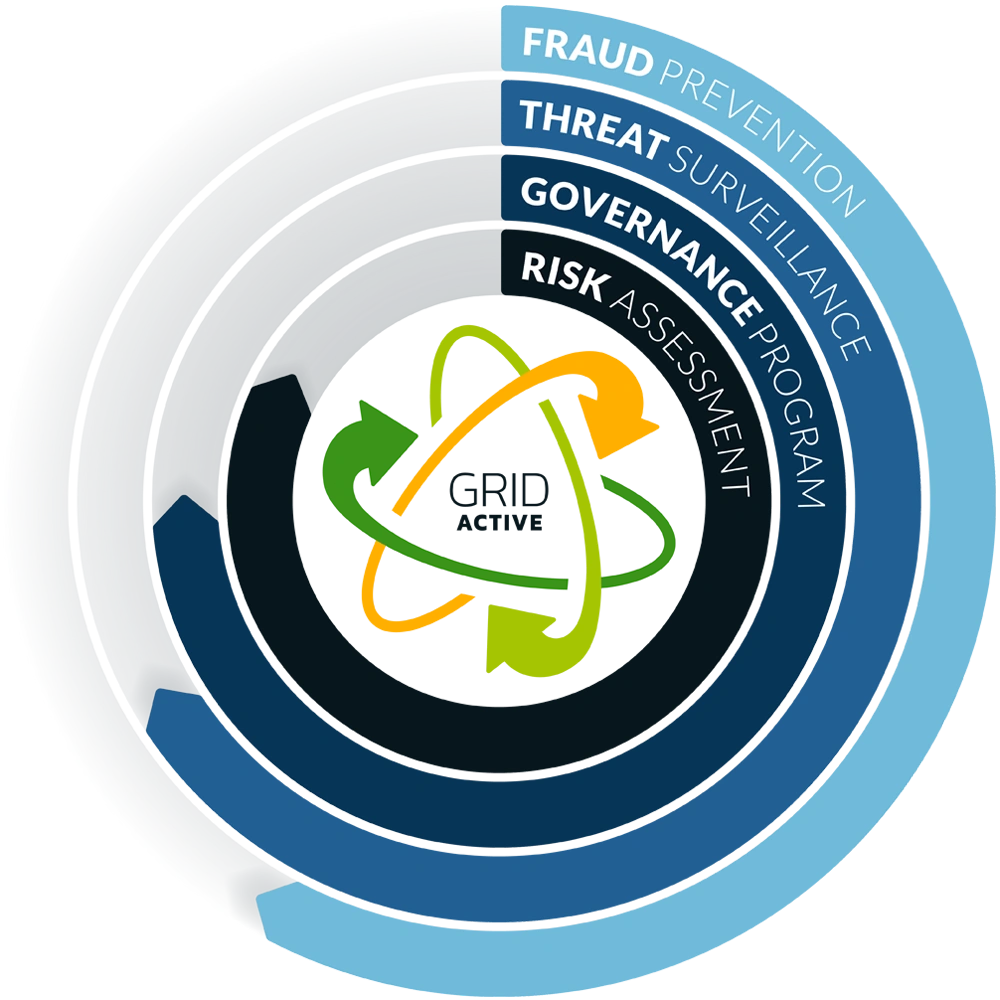
Cyber Risk Readiness Action Dashboard LIVE in GRID Active
Announcing the NEW GRID Active Cyber Risk Readiness Action Dashboard. The additions to DefenseStorm’s Cyber Security Risk Management platform delivers customers with an overview and actionable steps to stay ready against cyber attacks

Blogs
Cybersecurity Assessment Tool (CAT) Sunset Announcement
The Federal Financial Institutions Examination Council (FFIEC) released important information surrounding the commonly used Cybersecurity Assessment Tool (CAT).

Case Studies
Georgia’s Own Credit Union
With over $4B in assets, Georgia’s Own Credit Union serves nearly 240,000 members across 37 offices. Georgia’s Own CU originally signed with DefenseStorm in 2021 and continues to work in partnership to maintain a robust cyber risk management program.

Case Studies
Peach State Bank and Trust Testimonial
Peach State Bank and Trust has been a long-term, valued client of DefenseStorm since 2016, when the two companies first partnered. John Chapman, Information Security Officer at Peach State Bank and Trust sat with DefenseStorm during the 2023 Client Appreciation Event to discuss the importance of cybersecurity for their financial institution and the benefits of partnering with DefenseStorm.

Case Studies
A Regional Bank in the Midwest Improves Cyber Risk Readiness with DefenseStorm
A regional bank in the Midwest was functioning with two prime challenges. First, they had various different systems with which they managed risk – from risk assessments in one platform to managing network detection tools in another to different platforms for endpoint antivirus. The second issue and what motivated them to begin seeking another cyber risk management solution was that their current vendor for managed detection and response had lost the “personal touch” they desired.

Case Studies
Listerhill Testimonial
Listerhill Credit Union is guided by core values that include prioritization of safety and soundness in cybersecurity. Listerhill CU’s VP of Network Administration and Information Security Officer sat for an interview with DefenseStorm during the 2023 Client Appreciation Event to express their confidence in the ability to rely on a partner like DefenseStorm.

Threat Alerts
What to Know about the NPD Breach
In April 2024, a known threat actor calling themselves USDoD claimed to possess and sell approximately 2.9 billion records from National Public Data, which included individuals’ personal data from people in the US, UK, and Canada.

Threat Alerts
AT&T Unlawful Access of Customer Data Incident
News is emerging about AT&T’s disclosure of what they term as ‘Unlawful Access of Customer Data.’ The majority of AT&T customer data was illegally downloaded from their workspace on a third-party cloud platform from May 2022 through October 31, 2022 and on January 2, 2023.

Blogs
Cyber Risk Readiness in GRID Active
GRID Active now offers customer a view into their state of Cyber Risk Readiness and demonstrates the positive impact an integrated cyber risk management platform can have in managing cyber risk.

Threat Alerts
Evolve Bank and Trust Breach
In late June 2024, LockBit cybercriminal group claimed responsibility for having breached a government agency with plans to release the stolen data. It was revealed that the group actually breached Evolve Bank and Trust.

Blogs
Creating a Proactive Cybersecurity Risk Management Plan
Cybersecurity risk management is a critical component of risk for banks and credit unions and by taking a proactive approach to risk, you can identify, mitigate, and even prevent risk before it’s too late. Learn how DefenseStorm’s built for banking approach can help you tackle cybersecurity risk and keep your institution cyber risk ready.

Blogs
Cybercriminals Love the Olympics Too, but for Different Reasons.
The Olympic Games begin July 26, 2024, and end August 11, 2024. I, like most people around the globe, will be watching and cheering on our nation’s athletes as they achieve their goals and live out their Olympic dreams. Unlike most of the audience, though, I will also be thinking about the unseen but expected threats and attacks that will be occurring from cybercriminals and bad threat actors taking advantage of such a major event.

Blogs
Cybersecurity Risk 2024: Keeping Pace with Evolving Standards
A proposed rule from the Federal Deposit Insurance Corporation (FDIC) will establish new regulatory standards and increase the focus of cybersecurity risk management and governance while bringing an expectation of faster response times and real-time remediation of deficiencies.

Threat Alerts
Everything You Need to Know About the Alleged AT&T Data Leak
Reports of a massive AT&T data leak have surfaced, with around seventy million customers potentially affected. The data is reportedly for sale on a leak forum or website.
