DEFENSESTORM
Thought leadership and customer testimonials are some of the many ways we build a community of trust. These cybersecurity resources highlight our recent research and success stories.


Blogs
The DefenseStorm Cyber Threat Surveillance (CTS) Operations team monitors financial institutions 24/7/365, acting as a collaborative extension of each institution’s security staff. CTS Ops analysts engage directly with our clients on potential and realized cases giving them deep insight into attacks impacting the financial industry vertical.

Blogs
The banks walking out of their 2026 exams with the shortest exit meetings usually have one thing in common: a risk management program that can be defended in the room. The focus of the exam has become more about risk and governance than technical controls, and the examiners are more capable of putting risk management into technical context than they were two years ago.

Blogs
The credit unions walking out of 2026 exams with the cleanest results have one thing in common: a risk management program that can be explained and defended when the examiner asks. A program that’s living, evidenced, and governed at the board level.

Blogs
Last week, I hosted a webinar with Roger Grimes of KnowBe4 on AI-powered social engineering and deepfakes. His most uncomfortable takeaway was also the simplest: social engineering is already involved in most successful breaches, and AI is making the attacks that work even better.
Blogs
Your MDR vendor is probably great at catching threats. But can they speak examiner language?
Blogs
Nacha has released the 2026 Operating Rules and Regulations, and DefenseStorm breaks down the key points you need to know.

Blogs
As you prepare for the holidays, it’s important to remember that cybercriminals are preparing too! Now is the perfect time to strengthen your cybersecurity! Here are some important tips to keep your data and devices safe while you enjoy the holidays!

Blogs
Boards demand clarity on security, proof, and risk. Learn how banking-specific MDR delivers the metrics, evidence, and insight CISOs need to lead with confidence.

Blogs
Discover how tabletop exercises turn your financial institution’s incident response plan into real-world readiness, ensuring your team is prepared to protect trust, minimize chaos, and respond confidently when every second counts.

Blogs
Year after year, the data tells the same story: people remain the prime target in cyberattacks. Now, with attackers using AI to clone voices and craft convincing scams, the human element has become both our greatest risk and greatest opportunity. That’s why we’re revisiting the article, “The Human Firewall: Strengthening the Weakest Link in Cybersecurity,” because the strongest defense in 2025 is still built on the collaboration of technology, culture, and leadership to strengthen the human firewall.

Blogs
Generic cybersecurity solutions may look strong on paper, but for banks and credit unions they leave dangerous gaps. This blog exposes the illusion of “all-in-one” MDR services and explains why financial institutions face unique threats that generic models can’t handle.
Blogs
As businesses continue to embrace remote work and digital collaboration in 2025, Remote Access Tools (RATs) have become essential for maintaining productivity and supporting distributed teams. Yet, these powerful platforms also present a growing security challenge, as cybercriminals increasingly exploit vulnerabilities, misconfigurations, and user trust to infiltrate networks.
Blogs
Lumma Stealer—a powerful information-stealing malware that has wreaked havoc across the globe—made headlines in 2025. The Malware-as-a-Service (MaaS) platform, also known as LummaC2, allows cybercriminals to rent and deploy malware designed to steal sensitive information from infected devices. First surfacing in 2022, it has rapidly evolved into one of the most notorious info stealers on the dark web.

Blogs
With recruiters using LinkedIn as a very popular way to research and reach out to potential candidates, bad actors have begun to try to abuse people’s trust and desire for new challenges to lure them in with fake job opportunities as a way capture their credentials and deliver additional malware.
Blogs
The IRS has already made several reminders for individuals to be aware of bad actors trying to take advantage of this season to gain access to your personal data and finances. Read tips and guidance taken directly from the IRS’ website, including associated links to stay safe during tax season.

Blogs
Take a minute and think about the password(s) you use in both your professional and personal capacities. When passwords are reused or weak, they are far more susceptible to being stolen. One stolen password can lead to a detrimental data breach for your organization.

Blogs
To prepare for the FFIEC Cybersecurity Assessment Tool sunset date, financial institutions should identify a new framework around which to build their programs and self-assess themselves against that framework using a risk based approach to ascertain that the appropriate level of maturity is reached within various areas.

Blogs
With the remote workforce not showing any signs of slowing down, many organizations are starting to evaluate and implement ways to access these systems through the usage of Remote Access Tools. While these tools provide an incredible amount of value to an organization to stay connected and retain access, Remote Access Tools are a significant attack vector in cybersecurity and are something that should not be taken lightly.
Blogs
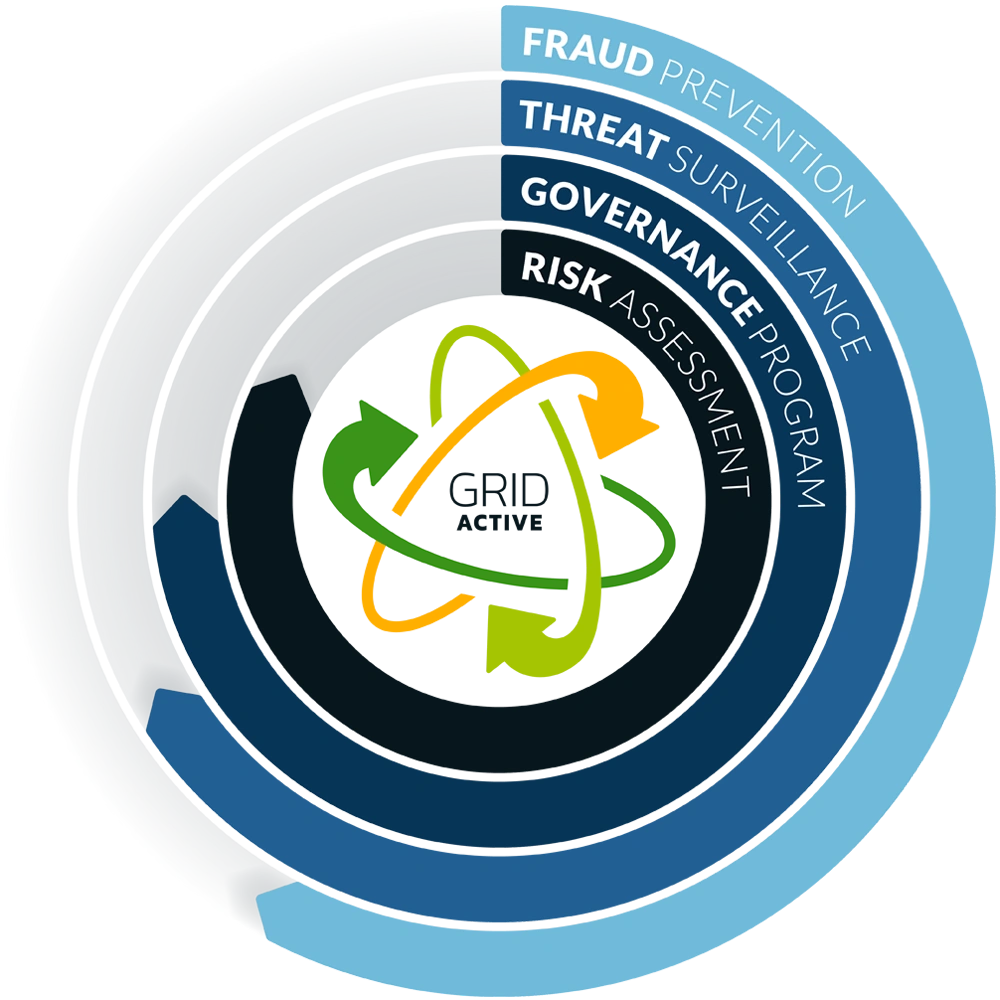
Announcing the NEW GRID Active Cyber Risk Readiness Action Dashboard. The additions to DefenseStorm’s Cyber Security Risk Management platform delivers customers with an overview and actionable steps to stay ready against cyber attacks

Blogs
The Federal Financial Institutions Examination Council (FFIEC) released important information surrounding the commonly used Cybersecurity Assessment Tool (CAT).

Blogs
GRID Active now offers customer a view into their state of Cyber Risk Readiness and demonstrates the positive impact an integrated cyber risk management platform can have in managing cyber risk.

Blogs
Cybersecurity risk management is a critical component of risk for banks and credit unions and by taking a proactive approach to risk, you can identify, mitigate, and even prevent risk before it’s too late. Learn how DefenseStorm’s built for banking approach can help you tackle cybersecurity risk and keep your institution cyber risk ready.

Blogs
The Olympic Games begin July 26, 2024, and end August 11, 2024. I, like most people around the globe, will be watching and cheering on our nation’s athletes as they achieve their goals and live out their Olympic dreams. Unlike most of the audience, though, I will also be thinking about the unseen but expected threats and attacks that will be occurring from cybercriminals and bad threat actors taking advantage of such a major event.

Blogs
A proposed rule from the Federal Deposit Insurance Corporation (FDIC) will establish new regulatory standards and increase the focus of cybersecurity risk management and governance while bringing an expectation of faster response times and real-time remediation of deficiencies.

Blogs
NIST’s Cybersecurity Framework (CSF) is designed to help institutions of all sizes and sophistication levels manage and reduce their unique cybersecurity risks. With the release of CSF 2.0, the guidance provided by NIST has expanded the practice and controls that institutions can use to best understand, assess, prioritize, and communicate its cybersecurity efforts.

Blogs
Cyber scams and election season just go together, and as election season begins to ramp up, so will cyber scams and the variety of tactics that bad actors will deploy in the attempt to obtain your personal information.

Blogs
Banking trojans continue to evolve and succeed due to their ability to persist, bypass security, and evade detection on mobile devices. As investment from fast-moving threat actors continues to increase, traditional security practices are unable to keep up.

Blogs
DefenseStorm has made a cyber security software update to our GRID Active Governance Program with new functionalities, further enhancing its capabilities as a powerful cyber risk management solution. Organizations now can link dashboards to task schedules for scheduling and documenting report reviews.

Blogs
DefenseStorm’s cyber risk assessment solution has recently been updated with new functionalities, further enhancing its capabilities as a powerful cyber risk management solution with GRID Active Risk Assessment Exceptions.

Blogs
Keeping up with cyber security alerts is important and Apple just rolled out a new default feature for iPhone and Apple watch that allows nearby users to share contact information with one another. This feature has sparked some concern in online social communities and even prompted law enforcement agencies to release statements and privacy warnings over the last few days due to the concern that people could “drop” information on another user’s phone at random, which seems scary.