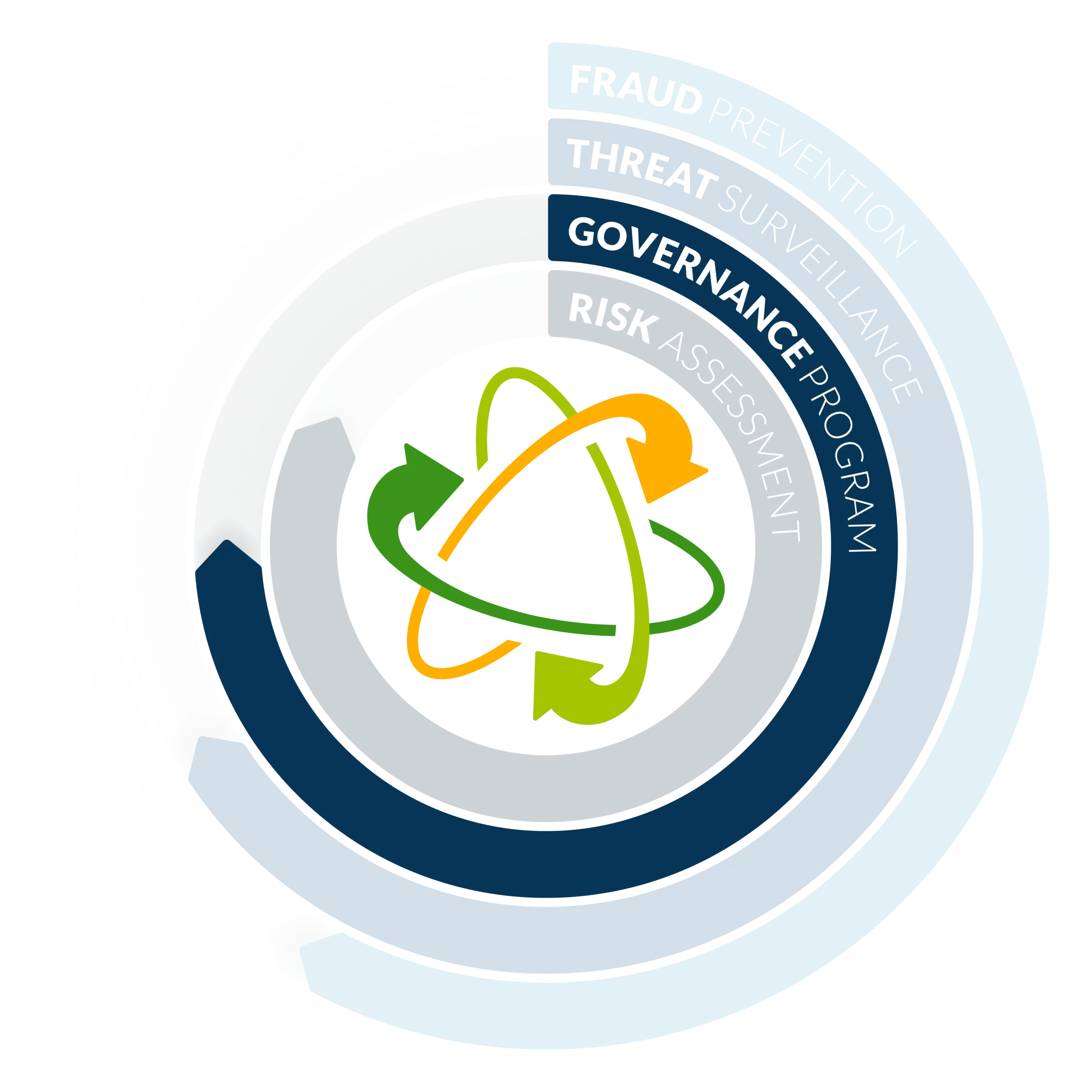
INTEGRATED CYBER RISK MANAGEMENT PLATFORM
Getting ready for an audit or exam is time-consuming, stressful and often a very manual process. GRID Active Governance Program allows financial institutions to monitor the effectiveness of their cybersecurity compliance and cyber risk management program, with automated evidence collection processes that proves adherence to regulatory control frameworks and simplifies audit and exam preparation with our built for banking approach.


You need the ability to conduct ongoing cybersecurity compliance monitoring for adherence to your internal policy and process, industry control frameworks and regulatory requirements to bridge the gap between typically siloed teams – like IT, information security and risk. Full understanding of where you stand in your cybersecurity compliance to self-assessment frameworks, like the FFIEC’s CAT (Cybersecurity Assessment Tool) allow you to better manage your cyber risk.
GRID Active Governance Program allows you to monitor the effectiveness and compliance of your cyber risk management program with automated evidence collection processes that proves adherence to regulatory control frameworks and simplifies audit and exam preparation. With a built for banking approach to improve cybersecurity risk management, you have the ability to understand your cyber risk readiness in real time, like you can with any other financial risk.
To further cyber risk readiness, align your risk management and governance with our GRID Active Risk Assessment and Governance Package. By combining these solutions, you’re able to prove evidence of the effectiveness of controls in your risk assessment and support residual risk scores, while demonstrating adherence to cybersecurity frameworks, including:
You can leverage pre-mapped Task Schedule templates to schedule program activities to save time and remain within framework guidelines since activities map automatically and directly into framework and self-assessment directives as evidence. You have full access to your log data to complete governance and monitoring activities through GRID Active, our integrated data platform to improve your cybersecurity compliance.
You have full control to schedule governance and monitoring activities to align with your cybersecurity compliance program cadences. You have access and can leverage your data through GRID Active to conduct monitoring and governance actions and memorialize reviews – all to better demonstrate adherence to your cybersecurity compliance and risk program.
Prove your cybersecurity compliance controls align with regulatory requirements and industry best practices through a curated library of pre-mapped templates shaped from regulatory requirements, industry best-practices, and examiner expectations. Guide your program oversight with self-assessment tools for measuring the state of your program. The GRID Active integrated data platform systematically collects evidence to support industry and regulatory control frameworks so you can monitor your cybersecurity compliance program against unlimited frameworks.

GRID Active Reporting enables financial institutions to exercise informed decision-making through consistent metrics and ensure confidence in the execution of strategic risks.
Through strong reporting, FIs can customize their reports based on audience and timing to better demonstrate the overall cybersecurity compliance risk objectives are being met.



