DEFENSESTORM BLOG
Monday, September 11th, 2023

Business email compromise (BEC) is a type of cyberattack that usually occurs through some type of social engineering campaign where the criminals assume the identity of a trusted person or organization and attempt to influence their victims into providing money through transfers or other digital payments, divulging personal information, making phony purchases, providing credentials to accounts, etc
Business Email Compromise (BEC) is a type of cyberattack that usually occurs through some type of social engineering campaign where the criminals assume the identity of a trusted person or organization and attempt to influence their victims into providing money through transfers or other digital payments, divulging personal information, making phony purchases, providing credentials to accounts, etc. These attacks often come through phishing or smishing campaigns, and financial institutions (FIs) are major targets due to access to funds and the ease with which FIs can transfer those funds. There are several types of BEC Scams, and below are a few listed by the FBI:
BEC attacks can and will often lead to Email Account Compromise (EAC), which is frequently associated with and can perpetuate BEC. EAC and BEC statistics are often lumped together, but they should be viewed differently for several reasons, which will be discussed later.
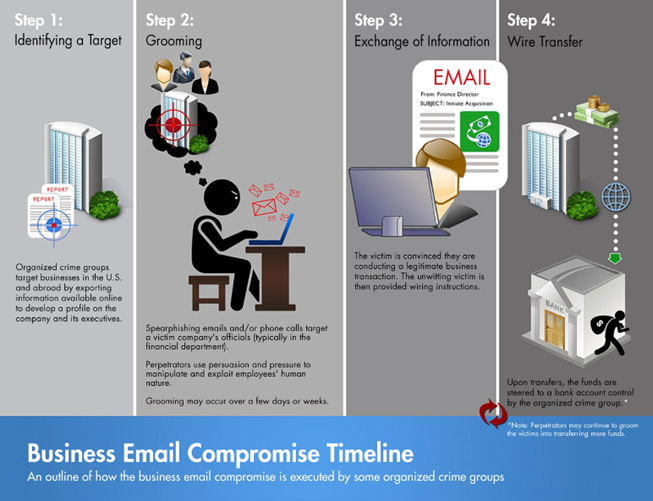
With a true BEC attack, minus email account compromise, there is usually an established timeline or process that takes place. The FBI provides a good graphic that depicts the steps.
As mentioned earlier, Business Email Compromise can lead to Email Account Compromise, and in turn, EAC can perpetuate BEC. These two types of attacks are so intertwined, that the FBI will even group these two together for statistical reporting, and they often have the same objective. That being said, there are some differences that need to be discussed, and the grouping of these two compromises seems to be a trend that is fading.
In a vast the major of BEC incidents, the attack will usually start with someone pretending to be you by looking very similar to you, like in domain spoofing or a vendor impersonation style attack. With EAC, the attackers ARE YOU! They have taken over a legitimate account and are using your account, credentials, access, and privileges to sustain and continue malicious/criminal behavior. They can now bypass traditional detection and Multi-factor Authentication (MFA) controls and tools.
In BEC, the target is generally a business and CAN lead to account takeovers, but the end goal of what is usually financial gain can be obtained by social engineering, and the need to fully take control of an account is not always necessary.
Again, EAC can result from BEC, but not always. Attackers may target individuals through personal email, smishing, or obtain account credentials through an impersonated login page that a user may encounter just from general web browsing. Once an attacker has access to an account, they may exploit that account for financial gain through a BEC, but they can also use that account to begin a larger phishing campaign from that legitimate email account. They may also use that account to spread malware not only in your environment but also in your customer/clients’ environment.
Statistical Data
Most of what you hear in the news and media about cybersecurity seems to be a lot about ransomware. While ransomware is the number one concern on most security professionals’ minds, Business Email Compromise is something to keep top of mind as well. The FBI has dubbed it the “$50 billion dollar scam”. In June of 2023, the FBI’s IC3 released updated statistics from BEC attacks and the numbers are staggering.
Source: Business Email Compromise: The $50 Billion Scam
The BEC scam has continued to evolve, targeting small local businesses to larger corporations, and personal transactions. Between December 2021 and December 2022, there was a 17% increase in identified global exposed losses. In 2022, the IC3 saw an increase in BEC reporting with a nexus to the real estate sector and BEC incidents where funds were transferred directly to a cryptocurrency exchange, or to a financial institution holding a custodial account for a cryptocurrency exchange. (See also: PSA I-041321-PSA)
The BEC scam has been reported in all 50 states and 177 countries, with over 140 countries receiving fraudulent transfers. Based on the financial data reported to the IC3 for 2022, banks located in Hong Kong and China were the primary international destinations of fraudulent funds. These were followed by the United Kingdom, which often acts as an intermediary stop for funds, Mexico, and Singapore.
The following BEC statistics were reported to the FBI IC3, law enforcement and derived from filings with financial institutions between October 2013 and December 2022:
Domestic and international incidents: 277,918
Domestic and international exposed dollar loss: $50,871,249,501
The following BEC statistics were reported in victim complaints to the IC3 between October 2013 and December 2022:
Total U.S. victims: 137,601
Total U.S. exposed dollar loss: $17,328,435,141
Total non-U.S. victims: 5,892
Total non-U.S. exposed dollar loss: $1,454,028,296
The following BEC statistics were reported by victims via the financial transaction component of the IC3 complaint form, which became available in June 2016. The following statistics were reported in victim complaints to the IC3 between June 2016 and December 2022:
Total U.S. financial recipients: 74,121
Total U.S. financial recipient exposed dollar loss: $13,034,596,130
Total non-U.S. financial recipients: 21,122
Total non-U.S. financial recipient exposed dollar loss: $8,451,345,479
How Can You Protect Yourself
While ransomware incidents tend to dominate the cyber news cycles, business email compromise and email account compromise are just as dangerous. They are not necessarily technical attacks and rely on human interaction and deception, which make them hard to detect with traditional security controls, especially in the case of email account compromise. Following the suggestions above and remaining consistent with training your user base greatly reduces the chances of being victimized.